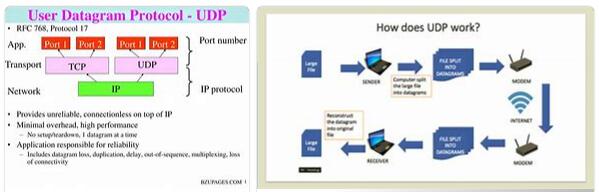
UDP (which stands for User Datagram Protocol according to abbreviationfinder) allows datagrams to be sent over the network without a connection having been previously established, since the datagram itself incorporates sufficient addressing information in its header. It also has no confirmation or flow control, so packets can preempt each other; and it is not known whether it has arrived correctly, since there is no confirmation of delivery or receipt.
Its main use is for protocols such as DHCP, BOOTP, DNS and other protocols in which the exchange of connect/disconnect packets are greater, or are not profitable with respect to the information transmitted, as well as for the transmission of audio and video in real time, where it is not possible to carry out retransmissions due to the strict delay requirements in these cases.
Description
UDP provides protocol ports used to distinguish between many programs running on the same machine. That is, in addition to the data, each UDP message contains both the destination port number and the source port number, making it possible for the UDP software at the destination to deliver the message to the correct recipient and for the recipient to send a response.
UDP uses the Internet Protocol (IP) as the underlying protocol to transport a message from one machine to another and, like it, provides a delivery service:
- Connectionless: It does not use acknowledgments to ensure that messages arrive, it does not order incoming messages, and it does not provide feedback to control the speed at which information flows between machines. Therefore, UDP messages may be duplicated or arrive out of order.
- Unreliable: An application program that uses UDP accepts full responsibility for handling reliability problems, including message loss, duplication, and delay, out-of-order delivery, and loss of connectivity.
UDP message format
- UDP message length (16 bits). Specifies the average length in bytes of the UDP message, including the header. Minimum length is 8 bytes.
- UDP checksum (16 bits, optional). Error checksum of the message. For calculation, a pseudo-header is used that also includes the source and destination IP addresses. To know this data, the UDP protocol must interact with the IP protocol.
- This is where the data sent by the applications travels. The same data sent by the source application is received by the destination application after traversing the entire network of networks.
UDP ports
UDP uses ports to allow communication between applications. The port field is 16 bits long, so the range of valid values is 0 to 65,535. Port 0 is reserved, but is an allowed value as a source port if the sending process does not expect to receive messages in response.
Ports 1 to 1023 are called “well-known” ports and on Unix-like operating systems binding to one of these ports requires super user access.
Ports 1024 to 49151 are registered ports.
Ports 49152 to 65535 are ephemeral ports and are used as temporary ports, mostly by clients when communicating with servers.
In practice, each application program must negotiate with the operating system to obtain a protocol port and associated port number before it can send a UDP datagram. Once the port is assigned, any datagram that the application program sends through it will have the port number in the UDP SOURCE PORT field.
While processing input, UDP accepts incoming datagrams from IP software and multiplexes them, based on UDP DESTINATION PORT.
The UDP port can be thought of as a queue. When an application negotiates port usage with the operating system, the operating system creates a buffer in memory and an internal queue that stores incoming messages. When UDP receives a datagram it checks if the destination port number corresponds to one of the ports that are in use. If that port number does not exist, it sends an ICMP port unreachable error message and discards the datagram. If it finds the port, UDP queues the new datagram on the port, waiting for the application to access it.
Sources
EVA, ICU. Lecture#5 UDP transport layer protocols. Teleinformatics II.
To eat. “Internetworking with TCP/IP. Volume I: Principle Protocols and Architecture”.